A tweet can contain up to 140 characters, a limit that is now relaxed, but if each character takes up 8 bits of information (one byte), the it can be said, a tweet is 140 bytes.
The Authorized version of the King James Bible contains 3,116,480 characters, or about 22,260 tweets. Some people have tweeted that much!
But all the information in the KJV pales compared to the information in every cell of the human body. The numbers will get large, so let us learn about large numbers
One kilobyte is 1000 bytes, Megabyte is 1000 Kb or 1000,000 bytes, Gigabyte is 1000 Mb or 1,000,000,000 bytes, Terabyte is 1000 Gigabytes or 1,000,000,000,000 bytes, Petabyte is 1000 Terabytes or 1,000,000,000,000,000 bytes, Exabyte is 1000 Terabytes or 1,000,000,000,000,000,000 bytes, Zettabyte is 1000 Exabytes or 1,000,000,000,000,000,000,000 bytes, Yottabyte is 1000 Zettabytes or 1,000,000,000,000,000,000,000,000 bytes.
 Back to how much data is in our body. We have about 3,2 billion DNA genome pairs in every cell in our body. there are 4 types, so each pair can be packed into 2 bits, which means every cell in our body contains 800 Megabytes of data, the information equivalent of 250 King James Bibles. Giving there are about 37 trillion cells in our body plus about one quadrillion bacteria in our gut the total amount of information in our body is about 30 Exabytes, most of it duplicated, but yet. In addition, all plants and animals contain DNA, so the total information in the world is staggering, far exceeding the term Yottabyte.
Back to how much data is in our body. We have about 3,2 billion DNA genome pairs in every cell in our body. there are 4 types, so each pair can be packed into 2 bits, which means every cell in our body contains 800 Megabytes of data, the information equivalent of 250 King James Bibles. Giving there are about 37 trillion cells in our body plus about one quadrillion bacteria in our gut the total amount of information in our body is about 30 Exabytes, most of it duplicated, but yet. In addition, all plants and animals contain DNA, so the total information in the world is staggering, far exceeding the term Yottabyte.
If you are an atheist or true believer in evolution that all this came about by chance plus time plus nothing, especially no sign of intelligent design, the math doesn’t add up.
In 2001 the New York City twin towers were destroyed through a terror attack, and the U.S. response was to collect data to capture terrorists before they could attack. The NSA started to monitor all electronic communication through a program called Prism, starting in earnest in 2007, see fig:
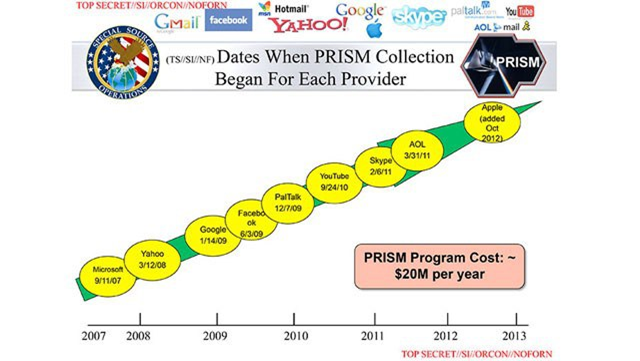
 This is in part taking place in a large data center in Utah, housing, it is rumored up to one Yottabyte of collected data.
This is in part taking place in a large data center in Utah, housing, it is rumored up to one Yottabyte of collected data.  What type of data do they collect? Check this figure:
What type of data do they collect? Check this figure:
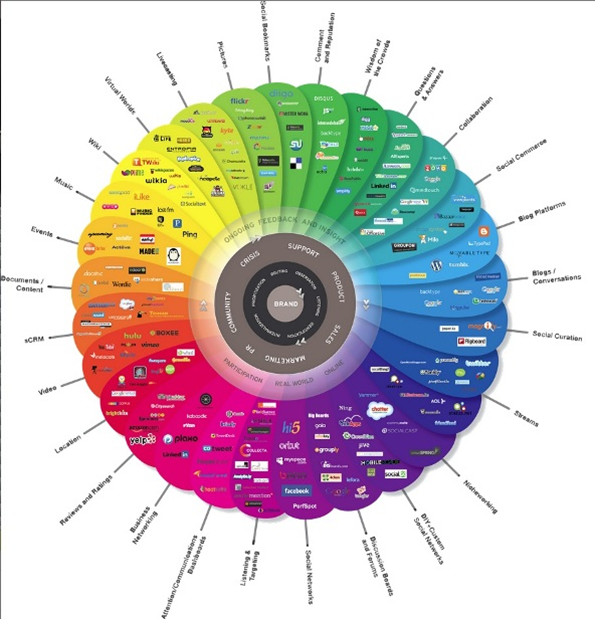 The question is this: How much of this is linked to terror?
The question is this: How much of this is linked to terror?
Then, today I found out via Wikileaks that NSA is not alone is spying on us.
CIA malware targets iPhone, Android, smart TVs
CIA malware and hacking tools are built by EDG (Engineering Development Group), a software development group within CCI (Center for Cyber Intelligence), a department belonging to the CIA’s DDI (Directorate for Digital Innovation). The DDI is one of the five major directorates of the CIA (see this organizational chart of the CIA for more details).
The EDG is responsible for the development, testing and operational support of all backdoors, exploits, malicious payloads, trojans, viruses and any other kind of malware used by the CIA in its covert operations world-wide.
The increasing sophistication of surveillance techniques has drawn comparisons with George Orwell’s 1984, but “Weeping Angel”, developed by the CIA’s Embedded Devices Branch (EDB), which infests smart TVs, transforming them into covert microphones, is surely its most emblematic realization.
The attack against Samsung smart TVs was developed in cooperation with the United Kingdom’s MI5/BTSS. After infestation, Weeping Angel places the target TV in a ‘Fake-Off’ mode, so that the owner falsely believes the TV is off when it is on. In ‘Fake-Off’ mode the TV operates as a bug, recording conversations in the room and sending them over the Internet to a covert CIA server.
As of October 2014 the CIA was also looking at infecting the vehicle control systems used by modern cars and trucks. The purpose of such control is not specified, but it would permit the CIA to engage in nearly undetectable assassinations.
The CIA’s Mobile Devices Branch (MDB) developed numerous attacks to remotely hack and control popular smart phones. Infected phones can be instructed to send the CIA the user’s geolocation, audio and text communications as well as covertly activate the phone’s camera and microphone.
Despite iPhone’s minority share (14.5%) of the global smart phone market in 2016, a specialized unit in the CIA’s Mobile Development Branch produces malware to infest, control and exfiltrate data from iPhones and other Apple products running iOS, such as iPads. CIA’s arsenal includes numerous local and remote “zero days” developed by CIA or obtained from GCHQ, NSA, FBI or purchased from cyber arms contractors such as Baitshop. The disproportionate focus on iOS may be explained by the popularity of the iPhone among social, political, diplomatic and business elites.
A similar unit targets Google’s Android which is used to run the majority of the world’s smart phones (~85%) including Samsung, HTC and Sony. 1.15 billion Android powered phones were sold last year. “Year Zero” shows that as of 2016 the CIA had 24 “weaponized” Android “zero days” which it has developed itself and obtained from GCHQ, NSA and cyber arms contractors.
These techniques permit the CIA to bypass the encryption of WhatsApp, Signal, Telegram, Wiebo, Confide and Cloackman by hacking the “smart” phones that they run on and collecting audio and message traffic before encryption is applied.
CIA malware targets Windows, OSx, Linux, routers
The CIA also runs a very substantial effort to infect and control Microsoft Windows users with its malware. This includes multiple local and remote weaponized “zero days”, air gap jumping viruses such as “Hammer Drill” which infects software distributed on CD/DVDs, infectors for removable media such as USBs, systems to hide data in images or in covert disk areas ( “Brutal Kangaroo”) and to keep its malware infestations going.
Many of these infection efforts are pulled together by the CIA’s Automated Implant Branch (AIB), which has developed several attack systems for automated infestation and control of CIA malware, such as “Assassin” and “Medusa”.
Attacks against Internet infrastructure and webservers are developed by the CIA’s Network Devices Branch (NDB).
The CIA has developed automated multi-platform malware attack and control systems covering Windows, Mac OS X, Solaris, Linux and more, such as EDB’s “HIVE” and the related “Cutthroat” and “Swindle” tools, which are described in the examples section below.
CIA ‘hoarded’ vulnerabilities (“zero days”)
In the wake of Edward Snowden’s leaks about the NSA, the U.S. technology industry secured a commitment from the Obama administration that the executive would disclose on an ongoing basis — rather than hoard — serious vulnerabilities, exploits, bugs or “zero days” to Apple, Google, Microsoft, and other US-based manufacturers.
Serious vulnerabilities not disclosed to the manufacturers places huge swathes of the population and critical infrastructure at risk to foreign intelligence or cyber criminals who independently discover or hear rumors of the vulnerability. If the CIA can discover such vulnerabilities so can others.
The U.S. government’s commitment to the Vulnerabilities Equities Process came after significant lobbying by US technology companies, who risk losing their share of the global market over real and perceived hidden vulnerabilities. The government stated that it would disclose all pervasive vulnerabilities discovered after 2010 on an ongoing basis.
“Year Zero” documents show that the CIA breached the Obama administration’s commitments. Many of the vulnerabilities used in the CIA’s cyber arsenal are pervasive and some may already have been found by rival intelligence agencies or cyber criminals.
As an example, specific CIA malware revealed in “Year Zero” is able to penetrate, infest and control both the Android phone and iPhone software that runs or has run presidential Twitter accounts. The CIA attacks this software by using undisclosed security vulnerabilities (“zero days”) possessed by the CIA but if the CIA can hack these phones then so can everyone else who has obtained or discovered the vulnerability. As long as the CIA keeps these vulnerabilities concealed from Apple and Google (who make the phones) they will not be fixed, and the phones will remain hackable.
The same vulnerabilities exist for the population at large, including the U.S. Cabinet, Congress, top CEOs, system administrators, security officers and engineers. By hiding these security flaws from manufacturers like Apple and Google the CIA ensures that it can hack everyone at the expense of leaving everyone hackable.
‘Cyberwar’ programs are a serious proliferation risk
Cyber ‘weapons’ are not possible to keep under effective control.
While nuclear proliferation has been restrained by the enormous costs and visible infrastructure involved in assembling enough fissile material to produce a critical nuclear mass, cyber ‘weapons’, once developed, are very hard to retain.
Cyber ‘weapons’ are in fact just computer programs which can be pirated like any other. Since they are entirely comprised of information they can be copied quickly with no marginal cost.
Securing such ‘weapons’ is particularly difficult since the same people who develop and use them have the skills to exfiltrate copies without leaving traces — sometimes by using the very same ‘weapons’ against the organizations that contain them. There are substantial price incentives for government hackers and consultants to obtain copies since there is a global “vulnerability market” that will pay hundreds of thousands to millions of dollars for copies of such ‘weapons’. Similarly, contractors and companies who obtain such ‘weapons’ sometimes use them for their own purposes, obtaining advantage over their competitors in selling ‘hacking’ services.
Over the last three years the United States intelligence sector, which consists of government agencies such as the CIA and NSA and their contractors, such as Booz Allan Hamilton, has been subject to unprecedented series of data exfiltrations by its own workers.
A number of intelligence community members not yet publicly named have been arrested or subject to federal criminal investigations in separate incidents.
Most visibly, on February 8, 2017 a U.S. federal grand jury indicted Harold T. Martin III with 20 counts of mishandling classified information. The Department of Justice alleged that it seized some 50,000 gigabytes of information from Harold T. Martin III that he had obtained from classified programs at NSA and CIA, including the source code for numerous hacking tools.
Once a single cyber ‘weapon’ is ‘loose’ it can spread around the world in seconds, to be used by peer states, cyber mafia and teenage hackers alike.
This is where we are today. On Saturday, President Trump found out that he had been spied upon in Trump Tower during the election. The Wikileaks revelation lends credibility to this accusation. And of course, CIA can make it appear that the hacking came from, say Russia and then put in some false software, framing the victim.
Yet, all this spyware, hacking and data gathering is simple compared to the wonder of life.